Cyber Insurance Not Paying Out?
Why Claims Get Denied (and How to Prevent It)
Index

Gordon B. Coyle
CEO, The Coyle Group
845-474-2924
How to get started
The Bottom Line
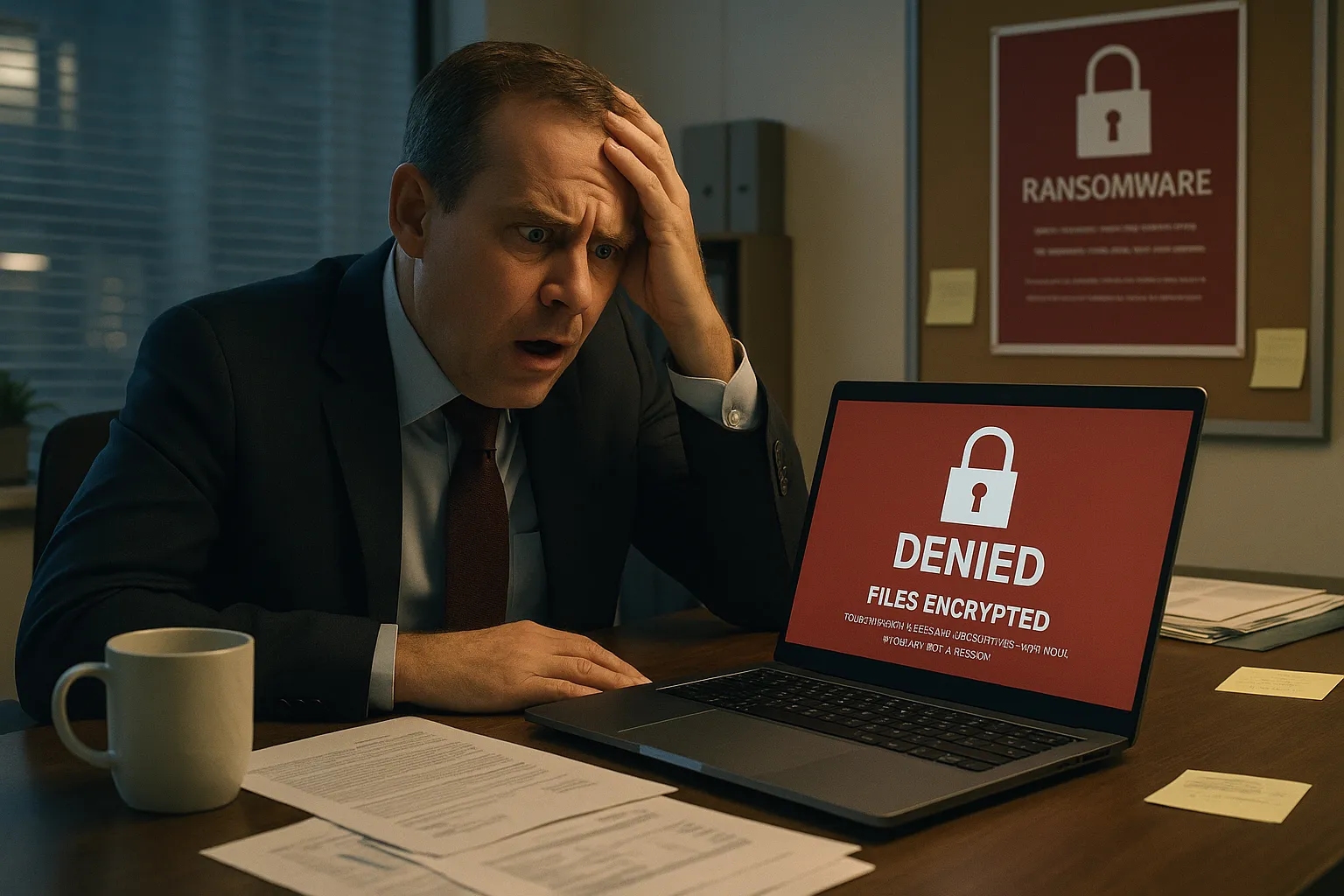
Your cyber insurance renewal arrived. The premium looked familiar. You signed. Six months later, a ransomware attack hits, and your claim gets denied.
Cyber insurance not paying out happens more often than decision makers realize.
According to Astra Security’s analysis of insurance data, 27% of data breach claims and 24% of first-party claims had exclusions within the insurance package that resulted in non-payout or partial payouts. Most denials are preventable, but SMBs don’t understand what voids coverage until they file a claim.
Key Takeaways:
To audit your coverage gaps
Understanding Key Terms
Before diving into why claims get denied, let’s define critical terms: understanding why cyber insurance not paying out is a common issue and what that means for policyholders.
Reason #1: Policy Exclusions You Didn’t Know Existed
Cyber insurance policies contain detailed exclusions that explicitly state what isn’t covered. Most SMBs don’t read them carefully, and even fewer understand how they apply to specific situations.
Common Cyber Insurance Exclusions:
What to Look for in Your Policy:
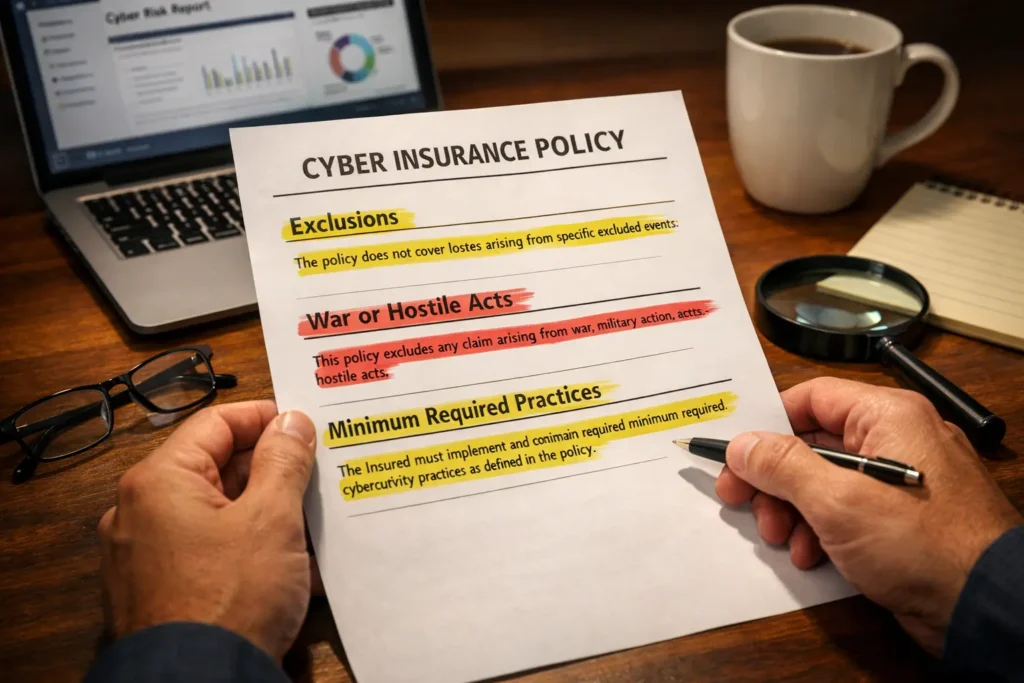
Real-World Impact: Mondelez vs. Zurich Insurance
During the 2017 NotPetya ransomware attack, Mondelez filed a $100 million claim. Zurich initially denied coverage, citing an “act of war” exclusion since the attack was attributed to the Russian military. The parties later settled with terms undisclosed, highlighting how war exclusion language creates coverage disputes in state-sponsored attacks.
War exclusions and ambiguous policy language create real financial exposure.
Reason #2: Coverage Lapses and Timing Issues
One of the most preventable reasons for cyber insurance not paying out is coverage gaps. Cyber insurance operates on a claims-made basis, not an occurrence basis. This distinction is critical.
How Claims-Made Coverage Works:
Common Coverage Gaps:
The Circumstances Reporting Option
Many policies allow you to report “circumstances that may give rise to a claim” before your policy expires. If you suspect an incident occurred but haven’t confirmed it, reporting it properly can preserve coverage even if the claim is filed after your policy ends. Check your specific policy language and notification requirements.
According to the NAIC’s 2025 Cyber Insurance Report, the number of claims rose almost 40% with nearly 50,000 reported in 2024, reflecting rising incident frequency, but gaps in coverage leave many businesses vulnerable.
Critical reminder
If you have a cyber incident during a period when you had no coverage, your claim will be denied. No coverage means no payout, period.
Understanding cyber insurance coverage basics prevents these timing vulnerabilities.
For a clear assessment of your protection status and potential denial triggers.
Reason #3: Failure to Maintain Required Security Controls
Many cyber insurance policies require you to maintain certain security controls as a condition of coverage. If you don’t maintain these controls, the carrier can deny your claim, citing non-compliance with policy requirements.
Required Security Controls (2026 Standards):
The Microsoft MFA statistic demonstrates why underwriters now treat multi-factor authentication as table stakes, not because it’s an insurance requirement, but because the risk reduction is so substantial that policies without MFA are effectively uninsurable at reasonable rates.
Real-World Example: International Control Services vs. Travelers
Insurance disputes have arisen where companies had MFA on their firewall but not on servers, email, or remote access as the policy required. The case illustrates how “scope of controls” matters, having MFA somewhere isn’t the same as having it everywhere your policy specifies.
Learn more about what MFA is and why it matters.

Reason #4: Misalignment Between What You Thought Was Covered and What Actually Is
This is perhaps the most frustrating source of cyber insurance not paying out; businesses discover coverage gaps only after filing.
Coverage Scope Confusion:
Ransomware Coverage
Business Interruption
Legal Defense
Common Coverage Gaps:
Coverage Type |
What’s Typically Included |
What Often Requires Endorsement |
Typical Sublimit |
|---|---|---|---|
|
Extortion/Ransomware |
Negotiation, response costs |
Actual ransom payment |
$250K-$1M |
|
Social Engineering/BEC |
Sometimes basic coverage |
Enhanced BEC/FTF protection |
$100K-$500K |
|
Dependent Business Interruption |
Rarely standard |
Contingent BI endorsement |
$500K-$2M |
|
PCI Assessments |
Limited or excluded |
Specific PCI endorsement |
$50K-$250K |
|
System Damage/Bricking |
Limited first-party |
Physical damage to systems |
Varies widely |
|
Reputational Harm |
PR costs often sublimited |
Crisis management services |
$25K-$100K |
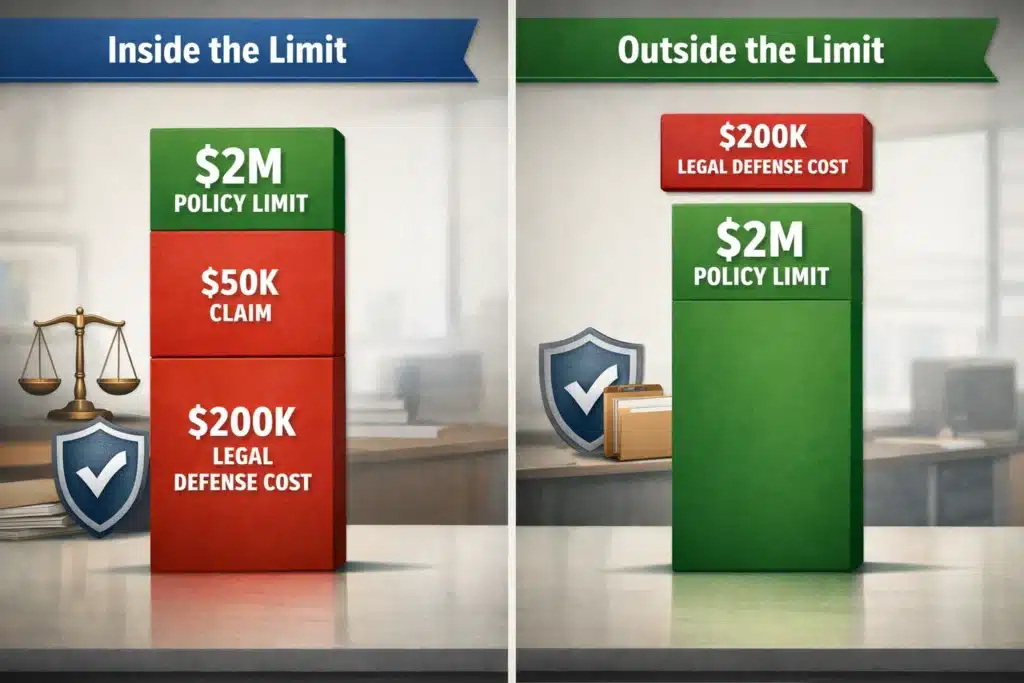
The “Inside vs. Outside” Defense Cost Issue
This is critical: When your policy says it provides “up to $2M in coverage,” does that include or exclude defense costs?
Most SMB policies have defense costs “inside the limit.” If you face a $50K incident but spend $200K on legal defense, you’ve used $250K of your limit, not $50K.
Real-World Example: Direct vs. Indirect Loss Disputes
Coverage disputes have arisen where business partners were compromised and funds fraudulently transferred. Carriers have denied claims stating the loss wasn’t “direct” since the partner was compromised, not the policyholder directly. The cases illustrate how social engineering coverage language varies significantly across carriers.
Understanding first-party vs third-party cyber coverages prevents these surprises.
That table probably surfaced 2-3 coverage assumptions you’re making right now
The Role of Policyholder Actions: What You Do Matters
Some cases of cyber insurance not paying out aren’t about policy language; they’re about what you did (or didn’t do) after an incident occurred.
Actions That Trigger Denials:

The Critical First 24 Hours Checklist:
According to the NAIC’s 2025 Cyber Insurance Report, nearly 50,000 claims were reported in 2024. Carriers are also getting more sophisticated at identifying policy violations.
These denials are within your control. They’re based on your actions or inactions after the incident occurs.
How to Protect Yourself: What Decision Makers Should Know
Understanding why cyber insurance claims get denied is the first step to preventing cyber insurance not paying out when you need it most.
Current Market Context: What the 2024-2025 Data Reveals
According to the NAIC’s 2025 Cyber Insurance Report, nearly 50,000 claims were reported in 2024, up almost 40% from 2023. Business Email Compromise (BEC) and ransomware remain the dominant drivers of claims, with ransomware inflicting the most financial damage per incident. Ransomware inflicts the most financial damage per incident. Understanding patterns of cyber insurance not paying out helps you avoid common pitfalls.
What This Means for Your Coverage:
Email-Based Attacks Dominate
BEC and Funds Transfer Fraud collectively represent a significant majority of claims. Many policies require specific endorsements for full BEC/FTF coverage rather than relying on standard computer fraud clauses.
Ransomware Remains Costliest
While frequency has moderated, ransomware attacks generate the highest average losses due to ransom payments, business interruption, forensic investigation, and digital asset restoration costs.
Security Controls Drive Pricing
The market is softening with rates declining, but security control requirements are tightening. Good controls = competitive pricing. Weak controls = higher premiums or denial.
Swift Reporting Matters
Industry data shows that prompt incident reporting significantly improves recovery rates for funds transfer fraud events, but only when incidents are reported quickly.
Understanding what social engineering is helps you address all email-based threats.
How The Coyle Group Prevents Claim Denials
We don’t just sell cyber insurance, we help you understand what you’re buying and ensure you can actually use it when needed.
Our approach includes:
Don’t wait until you’re filing a claim to discover:
95+
Years of Family Legacy in Insurance
40+
Years Personal Experience
95%
Client Retention Rate
600+
Educational Videos
Questions About Cyber Insurance Not Paying Out
The Real Question Isn’t “Will My Policy Pay?”, It’s “Can I Prove It Will?”
Most businesses assume their cyber insurance works. They paid the premium, they have the policy, they’re covered. Then a breach happens and the carrier asks for documentation they don’t have.
If your carrier called right now and asked you to prove:
…could you send them that documentation within 24 hours? If the answer is “probably not,” you’re one breach away from a denial letter.
We help businesses close that gap before it becomes a problem. Not with more insurance, but with better documentation and a clear understanding of what your current policy actually requires.

This article was written by Gordon B. Coyle, CPCU, ARM, AMIM, PWCA, CEO of The Coyle Group, who has over 40 years of experience working with business owners of all sizes and industries across the US, solving their insurance challenges. Gordon specializes in helping SMBs develop comprehensive cyber insurance programs that protect their operations and support their growth objectives.
Here’s how to take the next step
Schedule Your Insurance Confidence Assessment
In our 30-minute call, you’ll discover:
Not ready for a call?
Get Free Access to Our Gated Video:
“How to Finally Feel Confident in Your Coverage. “
And discover the exact system we use to help business owners eliminate hidden coverage gaps, stop overpaying, and finally feel confident in their protection.
What Peace of Mind Looks Like
Trusted by business owners across the U.S.
Want to know more?
See related blogs

The Crowdstrike Debacle and Cyber Insurance
Third Party Employment Practices Liability Insurance. Protect Your Business

Are You Overpaying or Underinsured on Your Business Insurance?



