Quick Answer
Data breach insurance is a type of business insurance that covers the direct costs of responding to unauthorized access or theft of sensitive business data, including notification expenses, forensic investigation, legal defense, and credit monitoring for affected individuals. For small businesses, standalone policies start at $1,000 to $5,000 per year. If your business stores customer data, employee records, or financial information, data breach insurance is not optional. It is essential.
Ready to get covered? Let us review your exposure and source the right policy
What Is Data Breach Insurance and Why Does Every Business Need It?
Data breach insurance protects your business from the immediate out-of-pocket costs that hit the moment a data incident is discovered. Most businesses assume their general liability or cyber policy covers this. Most are wrong, and the gap between what they have and what they actually need can cost millions before they realize it.
The Core Problem It Solves
When sensitive customer or employee data is accessed, stolen, or accidentally exposed, your business is legally required to act immediately: notify affected individuals, hire forensic investigators, retain legal counsel, and fund credit monitoring for victims. None of that is cheap. Data breach insurance is what pays for those costs before they drain your operating account.
Who Needs Data Breach Insurance?
If your business handles any of the following, you need this coverage:
The assumption that small businesses are “too small to target” is one of the most expensive myths in commercial insurance. Attackers specifically seek out smaller organizations because they typically lack dedicated security resources, making them far easier to breach than large enterprises. According to state data breach notification laws tracked by the National Conference of State Legislatures, all 50 states now require businesses to notify affected individuals after a breach.
How Much Does a Data Breach Insurance Actually Cost?
Most businesses pay $8,000 to $35,000 per year for data breach coverage, depending on industry, data volume, and security posture. Smaller risks with limited records and strong controls can come in below that. Complex risks, financial services, healthcare, and technology firms with large data stores often exceed it.
According to IBM’s 2025 Cost of a Data Breach Report, the global average cost fell to $4.44 million, but the US average hit a record $10.22 million, up 9% year over year. For American businesses, that’s the number that matters. Your actual costs depend heavily on industry, record volume, and how quickly a breach is detected and contained.
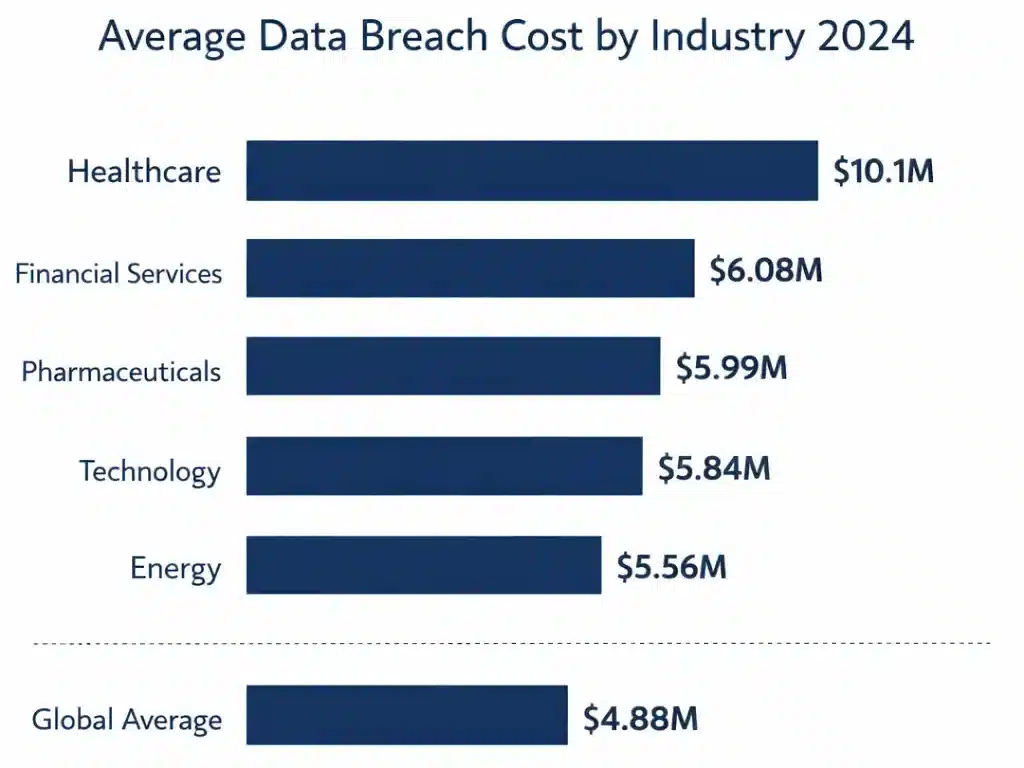
Industry Breach Cost Breakdown
Industry |
Average Breach Cost |
|---|---|
|
Healthcare |
$10.1 million |
|
Financial Services |
$6.08 million |
|
Pharmaceuticals |
$5.99 million |
|
Technology |
$5.84 million |
|
Energy |
$5.56 million |
|
Global Average |
$4.44 million |
What Actually Drives These Costs
What Determines Your Premium
Factor |
Impact on Premium |
|---|---|
|
Industry (healthcare, financial, legal) |
Highest premiums, regulatory exposure drives cost |
|
Record volume |
More records = higher notification cost exposure |
|
Security controls |
Missing MFA or EDR can add 25–50% to your quote |
|
Annual revenue |
Higher revenue = higher target value = higher premium |
|
Prior claims |
Any prior cyber claim will increase your rate |
The Per-Record Reality Check
Before you pick a coverage limit, run the math. IBM’s 2025 data puts notification and response costs at $160 per compromised customer record in the US. A business with 50,000 client records faces $8 million in notification costs alone, before legal, forensic, or business interruption costs are added. That’s why policy limits and sub-limits matter more than premiums when you’re evaluating coverage.
The right policy isn’t the cheapest one. It’s the one where the limits, sub-limits, and exclusions actually match your data footprint. Book a call to find out what your exposure actually looks like.
What Does Data Breach Insurance Cover?
Data breach insurance covers the immediate, first-party response costs your business incurs after a breach, but the specific components vary significantly between policies, and the sub-limits embedded in standard forms often fall short of real-world response costs. Knowing exactly what your policy covers before you need it determines whether you are protected or just insured on paper.
What Data Breach Insurance Covers: The Complete List
Understanding how cyber threat insurance broadens this protection helps you identify which gaps remain after a standard data breach policy.
First-Party vs. Third-Party Data Breach Coverage: What Is the Difference?
First-party coverage pays for costs your business incurs directly: notification, forensic investigation, credit monitoring, legal coordination, and business interruption. This is what most people mean when they say “data breach insurance.”
Third-party coverage pays for costs that arise when a client or vendor sues your business because a breach at your company affected them. This includes legal defense costs, settlements, and regulatory fines triggered by a third-party claim.
Standard data breach policies are first-party only. If your business handles data on behalf of clients, including any business processing customer information or operating under service agreements, third-party liability exposure is real and requires separate or broader cyber liability coverage.
Not sure which applies to your situation?
Data Breach vs. Cyber Liability vs. Crime Insurance: What Is the Difference?
These three coverages are routinely confused, and that confusion leaves businesses with dangerous gaps. The businesses that suffer the worst financial damage after an incident are almost always the ones that assumed one policy covered everything, without reading what was actually excluded from each form.
Coverage Type |
What It Pays For |
What It Does Not Cover |
|---|---|---|
|
Data Breach Insurance |
Notification costs, credit monitoring, forensic investigation, regulatory response, PR and crisis management |
Ransomware payments, wire fraud, employee theft |
|
Cyber Liability Insurance |
Everything above, plus ransomware payments, business interruption, network security liability, media liability |
Wire fraud (usually), employee theft, physical theft |
|
Crime Insurance |
Wire fraud, employee theft, forgery, computer fraud resulting in direct financial loss |
Notification costs, regulatory fines, reputational damage, breach response |
Data breach insurance is a core component of comprehensive cyber insurance coverage. A full cyber liability policy typically includes data breach coverage, but crime coverage for wire fraud, employee theft, and forgery requires a separate standalone form. If your broker offers a single policy that claims to cover “everything cyber,” ask specifically about social engineering fraud and employee theft limits.
Cyber vs. Crime Insurance: Understanding the Key Difference
What Data Breach Insurance Does NOT Cover
Standard data breach policies include exclusions that can eliminate coverage in the exact scenarios where you expect it most. The most dangerous gaps are not obvious at first glance. They appear in specific policy language around encryption requirements, prior knowledge provisions, and regulatory fine classifications that differ significantly by carrier and jurisdiction.
Important: Read the Exclusions Before You Bind
The cheapest premium almost always means the most exclusions. Prior known events, PCI fines, unencrypted device losses, nation-state attacks, and certain regulatory fines are commonly excluded. Verify each exclusion explicitly before binding your policy.
Why Human Error Makes Data Breach Insurance Essential
Everyone focuses on hackers, but human error accounts for 24% of all data breaches according to IBM’s 2024 research. This is the category most businesses are underinsured for, because leadership assumes coverage only applies to external cyberattacks. It does not, and that assumption is exactly where the most expensive gaps hide.
Real-World Example: $1.2M From One Wrong Email Attachment
During tax season, a staff member at a 35-person accounting firm attached the wrong PDF to a client email. Instead of one client’s quarterly filing, they sent a document containing detailed financial records for 100 top clients: names, Social Security numbers, business EINs, and income summaries. The document landed in a shared inbox at another company, accessible without a password.
Total damage: $1.2 million in breach-related costs, four high-revenue client relationships lost (worth $400,000 per year annually), and a cyber policy with only a $500,000 limit, leaving a $700,000 gap paid entirely out of pocket. This was not a cyberattack. It was a routine mistake by a trained professional.
A thorough cyber risk assessment before you shop for coverage quantifies your actual exposure before a mistake like this forces the calculation under pressure.
How to Choose the Right Data Breach Insurance Policy
Selecting the right data breach insurance policy is more complex than comparing premiums. The limits, sub-limits, exclusion language, and insurer response capabilities all vary in ways that only become visible when a claim is filed, and that is not when you want to discover your coverage falls short of your actual exposure.
Step 1: Inventory Your Data
Identify every type of sensitive data your business holds: PII, protected health information, financial account data, and business confidential information. You cannot select appropriate limits without knowing your actual exposure.
Step 2: Calculate Realistic Limits
Multiply your record count by $200 to $500 per record for notification costs, then add a 200 to 300% buffer for legal, regulatory, and business interruption costs. A firm with 10,000 client records should target $5 to $10 million in coverage minimum.
Step 3: Evaluate Insurer Quality
Look for a 24/7 breach response hotline, pre-approved vendor networks for forensic and legal response, proactive risk management resources, and a documented track record of efficient claims handling.
Understanding the full process of shopping for business insurance helps you evaluate coverage options across the market rather than defaulting to the first quote received.
How Technology Is Changing the Data Breach Landscape
The cyber threat environment in 2025 looks fundamentally different from two years ago. AI-powered defenses are cutting breach costs and accelerating detection times, but attackers are evolving in parallel, and the environments where data now lives have become substantially more complex to secure, monitor, and insure adequately.
What AI-Powered Security Actually Delivers
Organizations using AI and automation for security prevention save an average of $2.22 million per breach compared to organizations without these tools. Companies that fully deploy AI and automation see a 61-day reduction in breach containment time and a 42% internal detection rate (up from 33% the prior year). Detecting a breach internally rather than having a third party report it saves approximately $1 million per incident in response costs alone.
The Threat Vectors Growing Fastest
Understanding the ransomware problem driving breach costs is essential context for any business evaluating data breach insurance coverage in 2025.
Building a Complete Protection Strategy
Data breach insurance is a critical layer, but it does not work in isolation. The businesses that minimize breach costs consistently are those that combine strong insurance coverage with proactive risk management, and understand exactly how their different policies interact when an incident actually occurs.
The Complete Cyber Protection Framework
For businesses carrying E&O insurance, understanding how cyber and professional liability coverage interact is essential. The anatomy of a cyber breach shows how quickly costs escalate at each stage of an incident, which is the most useful framework for understanding why coverage limits matter as much as coverage terms.
Why Work With an Independent Broker for Data Breach Insurance?
As an independent broker, The Coyle Group has access to the top-rated data breach and cyber insurance markets in the country. That means we compare policy language, not just premiums, across multiple carriers to find coverage that actually matches your exposure. You get the best available terms, not just whatever a single carrier is willing to offer.
Frequently Asked Questions About Data Breach Insurance
Business owners evaluating data breach insurance ask the same practical questions before buying. The answers below cut through the marketing language and address exactly what matters when you are comparing policies, calculating limits, or trying to understand how this coverage fits into what you already have.
Author’s Expertise
This article was written by Gordon B. Coyle, CPCU, ARM, AMIM, PWCA, CEO of The Coyle Group, who has over 40 years of experience working with business owners of all sizes and industries across the US, solving their insurance challenges.




