Quick Answer
Cyber threat insurance pays for the direct costs of cyberattacks on your business: ransomware negotiation and recovery, forensic investigation, business interruption losses, data breach notification, and third-party liability. For most small to mid-sized businesses, annual premiums run $1,000 to $7,500. The critical distinction: most cyber policies exclude social engineering wire fraud, which requires a separate crime policy. Understanding your specific coverage triggers before a claim determines whether your policy actually pays.
What Is Cyber Threat Insurance and Why the Terminology Matters
Cyber threat insurance is the commercial coverage category that pays for financial losses from cyberattacks on your business. The problem is that “cyber threat insurance,” “cyber insurance,” and “data breach insurance” are used interchangeably in sales conversations, and they are not the same thing.
Your policy does not respond to what you call the attack. It responds to whether the attack matches your insurer’s specific definition of a covered event.
A ransomware attack that triggers a “security failure” clause in one policy may fall under “system failure” in another. That distinction controls whether your claim gets paid or denied.
The FBI’s 2024 Internet Crime Report documented $16.6 billion in cybercrime losses, with ransomware complaints increasing 9% year-over-year. Business email compromise alone caused $2.9 billion in losses. Most of that money came from businesses that assumed their coverage was broader than it actually was.
Gordon explains first-party vs. third-party cyber insurance coverage in plain terms
What Cyber Threats Actually Cost Businesses
Before evaluating a cyber threat insurance policy, you need to understand your actual financial exposure. The numbers are not theoretical.
How much financial exposure do you actually carry?
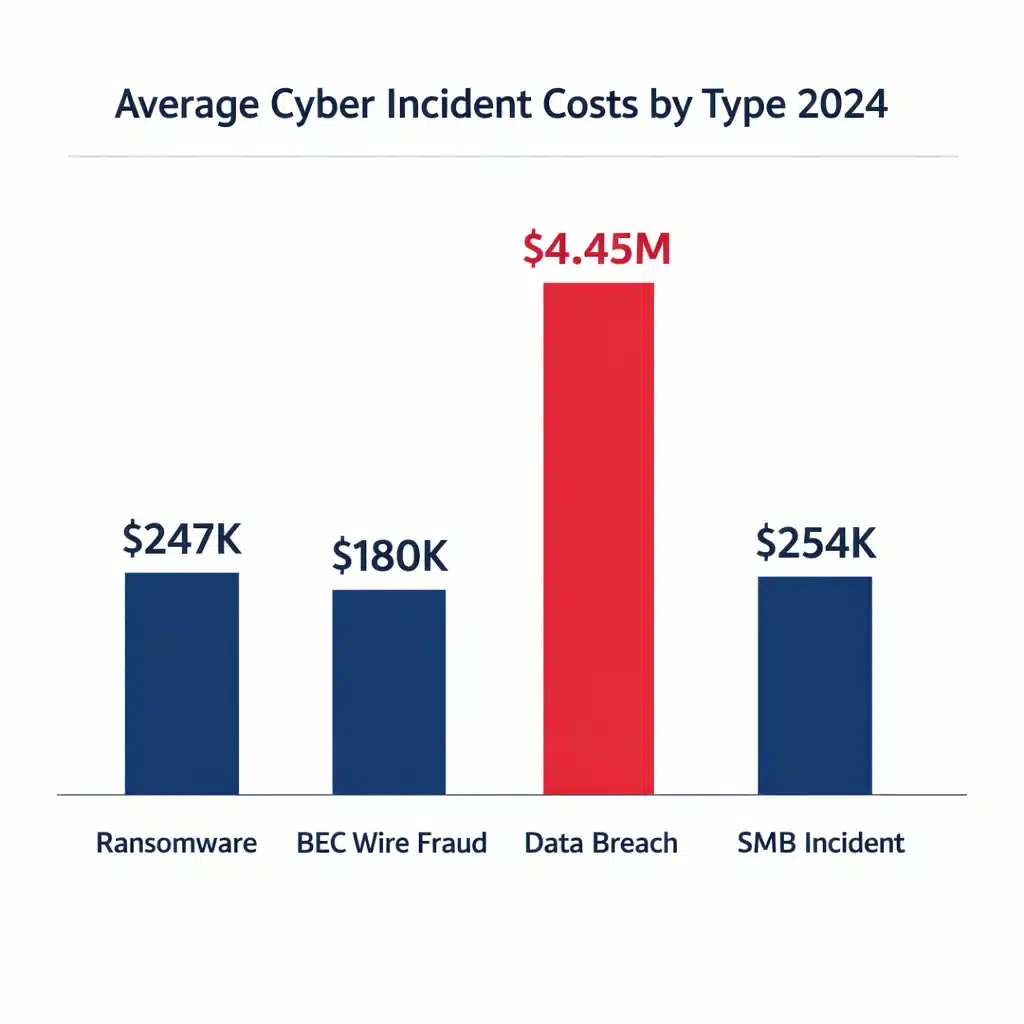
The global average data breach cost reached $4.45 million in 2024, but for SMBs the average incident runs $254,445 with individual cases reaching $7 million. The specific cost driver varies by attack type, and understanding which category hits your business hardest is what determines whether your coverage limits are adequate.
First-Party vs. Third-Party Coverage: What Each Actually Pays
Cyber threat insurance operates across two coverage tracks. Knowing which track responds to which loss determines whether you have the right policy structure.
First-party coverage pays your direct costs. Third-party coverage handles claims made against you. Most businesses focus on the first and underestimate the second until a customer lawsuit arrives.
First-party coverage pays your direct costs:
Third-party coverage handles claims against you:
What Cyber Threat Insurance Does NOT Cover (Where Claims Get Denied)
Exclusions define when the policy actually works in your favor. Most claim denials trace back to gaps the insured never reviewed before signing.
Cyber policies are sold as comprehensive protection. The exclusions tell a different story. Social engineering, vendor outages, nation-state attacks, and security control failures are among the losses most likely to occur and least likely to be covered under a standard form.
What 40+ Years Taught Me About Claim Denials
In four decades insuring businesses, I’ve watched companies lose $500,000 claims because their policy excluded the exact event that hit them. A $3,000 policy that denies your claim isn’t cheaper than a $5,000 comprehensive policy. It’s a $3,000 mistake that cost you $500,000. The businesses that avoid denials read the exclusions section before buying, not after filing.
A thorough cyber risk assessment before purchasing coverage maps your actual exclusion exposure against your operational profile. A thorough review of data breach insurance requirements specifically helps you understand the notification cost layer that sits inside your cyber policy.
Cyber Insurance vs. Data Breach Insurance vs. Crime Insurance
Three coverage types, three different threat profiles. Assuming one covers the others is the most common and most expensive mistake in commercial cyber insurance.
Most businesses that suffer significant financial damage from cyber incidents carried only one of these three products. The gaps between them are where the real losses occur.
Coverage Type |
What It Pays For |
Critical Gaps |
|---|---|---|
|
Cyber Threat Insurance |
Ransomware, forensics, BI, data breach response, network security liability, regulatory defense |
Social engineering, wire fraud, employee theft |
|
Data Breach Insurance |
Notification costs, credit monitoring, forensics, regulatory response, PR |
Ransomware payments, extended BI, third-party liability |
|
Crime Insurance |
Wire fraud, social engineering, employee dishonesty, forgery, funds transfer fraud |
Breach notification, regulatory fines, reputational damage |
For a deeper look at how these coverages interact, Gordon breaks it down in this video:
Security Controls That Determine Coverage Eligibility
These are underwriting requirements, not suggestions. Missing any of them can disqualify your application or eliminate coverage for the incidents most likely to hit your business.
Carriers have tightened underwriting substantially since 2022. The controls that were “recommended” three years ago are now deal-breakers. Understanding the anatomy of a cyber breach shows why each of these controls targets a specific attack stage.

How to Calculate the Right Coverage Limits for Your Business
Guessing at coverage limits is how businesses end up with a $2M policy and a $6M claim. The calculation is straightforward if you work through it methodically rather than defaulting to a broker’s suggested band.
Your worst-case business interruption exposure, breach notification costs, extortion reality, and third-party contract obligations are the four variables that determine your actual coverage floor. Vendor contracts with specific insurance requirements override every other guideline in this calculation.
Business Profile |
Recommended Limits |
Rationale |
|---|---|---|
|
Small business, limited PII, strong backups |
$1M to $2M |
Covers incident response plus moderate BI |
|
Data-heavy operations, compliance requirements |
$2M to $5M |
Handles notification costs plus class actions |
|
High payment volume, regulated industry, large client base |
$5M to $10M+ |
Protects against aggregate third-party claims |
Understanding how to shop for business insurance helps you integrate cyber coverage into your overall program rather than treating it as a standalone purchase. If your business carries professional services, review how E&O insurance and cyber coverage interact before binding either.
Real Scenarios: Which Policy Actually Pays?
The three scenarios below represent the most common ways businesses discover they were underinsured. Each one traces to a coverage gap that was visible in the policy before the incident occurred.
Every claim denial involves a gap that existed at policy inception. The difference between covered and unrecovered losses is almost always a policy review that didn’t happen before the event.
Ransomware with Downtime
A manufacturing company is hit by ransomware. Systems are encrypted. Customer data is exfiltrated. Attackers demand $200,000. The company is down for 5 days. First-party cyber pays for forensic investigation ($80,000), extortion negotiation ($15,000), ransom payment if approved, and system restoration ($120,000). Business interruption pays lost profits during the shutdown minus the waiting period. Third-party privacy liability responds if customers sue. Regulatory defense covers any state attorney general investigation. Total covered with adequate limits: $400,000 to $800,000 or more. The key variables are the extortion sublimit and the BI waiting period.
Vendor Outage Takes You Down
A critical cloud provider suffers a ransomware attack. Your SaaS platform is offline for 14 hours. You lose $45,000 in daily revenue. Standard business interruption does not pay because you were not directly attacked. If the vendor was specifically scheduled on a dependent business interruption endorsement, coverage applies after the waiting period. With an 8-hour waiting period, you recover 6 hours of loss. With a 24-hour waiting period, nothing is covered. The lesson: vendor outage coverage requires vendor scheduling, and waiting periods define how much of a short outage is actually recoverable.
BEC Wire Fraud ($180,000)
A finance employee receives an urgent email appearing to come from the CEO, requesting an immediate wire transfer. The employee sends $180,000 to a fraudulent account. The cyber policy excludes social engineering or caps it at $25,000. The business had no crime policy. The full $180,000 is unrecovered. With a crime policy including social engineering coverage, the full $180,000 would have been covered. This is the most preventable loss type in commercial cyber insurance and the most common reason businesses regret their policy structure after an incident.
For a detailed breakdown of how costs escalate at each stage of an actual breach, see the anatomy of a cyber breach. For an overview of how ransomware specifically drives claims and recovery costs, read the $11.5 billion ransomware problem.
Frequently Asked Questions About Cyber Threat Insurance
Author’s Expertise
This article was written by Gordon B. Coyle, CPCU, ARM, AMIM, PWCA, CEO of The Coyle Group, who has over 40 years of experience working with business owners of all sizes and industries across the US, solving their insurance challenges.




