Cyber Insurance Social Engineering
Key Coverage Insights
Your Cyber Insurance Policy Won’t Cover Social Engineering Fraud (Here’s Why)
Index

Gordon B. Coyle
CEO, The Coyle Group
845-474-2924
How to get started
Executive Summary
A hacker impersonates your CEO and emails accounting, requesting an urgent wire transfer. Under time pressure, the employee approves it. $150,000 gone.
Or: A vendor impersonation sends an invoice requesting payment. Your accounts payable team processes it without catching the fraud. $50,000 transferred before anyone realizes the mistake.
Does your cyber insurance cover Social Engineering?
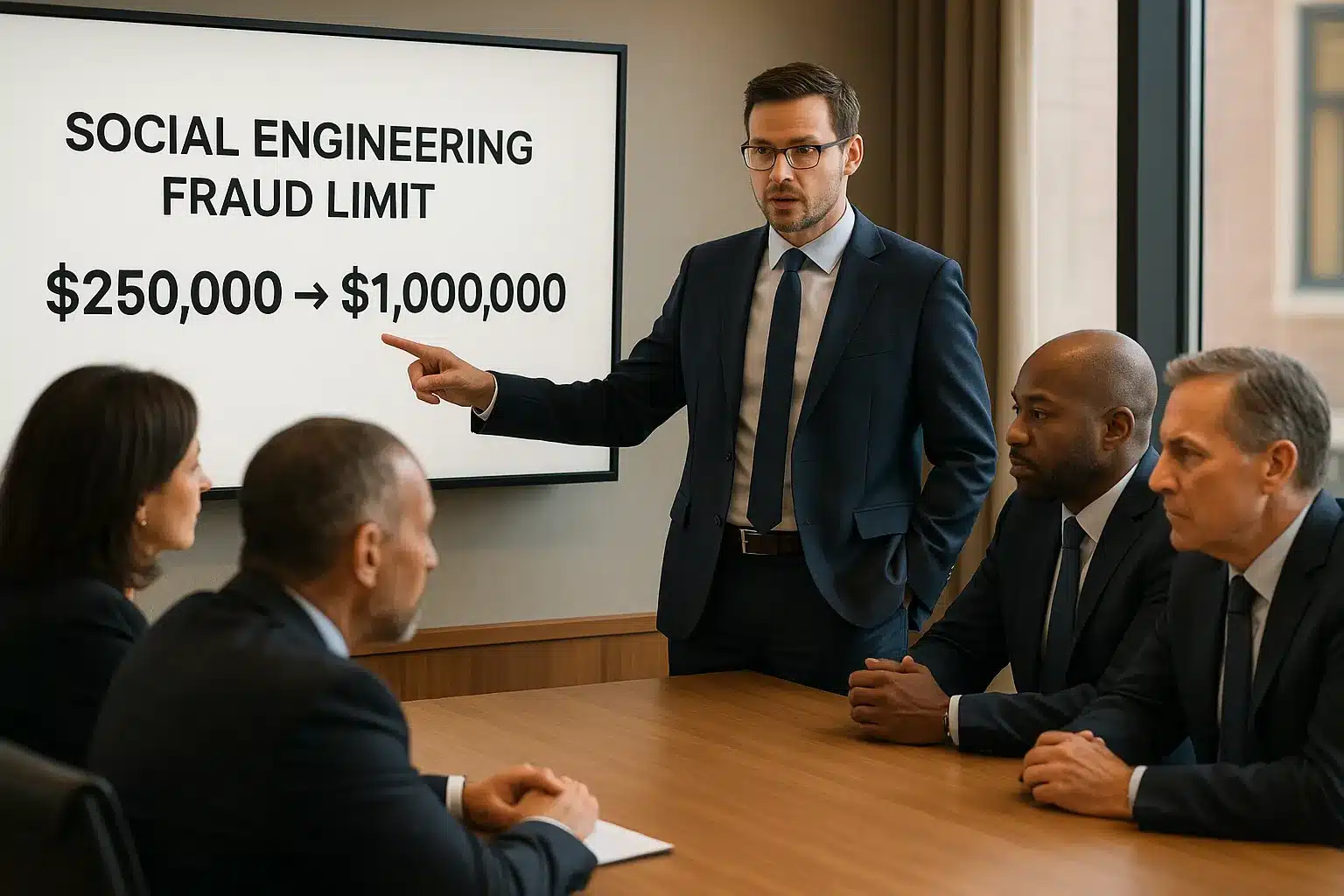
Yes, most policies include social engineering fraud coverage. But the coverage limit is almost certainly too low. Most cyber policies cap social engineering fraud at $250,000. If your exposure is higher, you’re underinsured.
The Bottom Line (TL;DR)
Your cyber insurance social engineering coverage demands strategic attention:
Investment range:
Additional $1,000–$5,000 annually to increase social engineering limits from $250K to $500K-$1M
Ready to assess your actual social engineering exposure? Schedule a coverage review to determine if your current limits match your risk. No obligation.
What Is Cyber Insurance Social Engineering Coverage?
Social engineering attacks exploit people through manipulation, impersonation, and fraud rather than technical vulnerabilities. Business Email Compromise (BEC), CEO fraud, vendor impersonation, fake invoice schemes, these attacks usually result in financial fraud rather than data theft.
Most cyber insurance policies include social engineering fraud coverage. Carriers recognize these attacks as legitimate cyber risks and have built coverage into standard policies.
The problem:
Coverage limits are inadequate. A single BEC attack can drain hundreds of thousands of dollars. If your policy caps social engineering coverage at $250,000 and you suffer a $400,000 loss, you absorb $150,000 out-of-pocket. This makes cyber insurance social engineering coverage critical
Coverage Structure Comparison
How Modern BEC Works, And Why AI Makes It More Dangerous
Business Email Compromise used to be straightforward: generic phishing emails hoping someone would click. Success rates were low.
Modern BEC is sophisticated. An attacker gains access to a company email account through a compromised password, phishing, or vendor access. Once inside, they observe. They monitor emails, study executive communication patterns, learn tonality, and understand approval workflows.
Then they draft an email that perfectly mimics that communication style. They understand what triggers urgency, which executives work together, and how your CFO phrases requests.
What 40+ Years Taught Me About This Risk
In four decades of helping businesses with insurance challenges, I’ve seen social engineering attacks evolve from crude scams to sophisticated operations. The businesses that avoid becoming victims treat social engineering coverage as a strategic component of their risk management, not an afterthought. They assess actual exposure, increase limits proactively, and maintain rigorous security controls.
AI accelerates this process. According to cybersecurity experts analyzing the 2024 FBI IC3 report, large language models analyze company email patterns and generate convincing impersonations automatically. Attackers feed AI samples of your CEO’s emails and generate new messages that sound exactly like your CEO, with perfect tone, phrasing, urgency, and style.
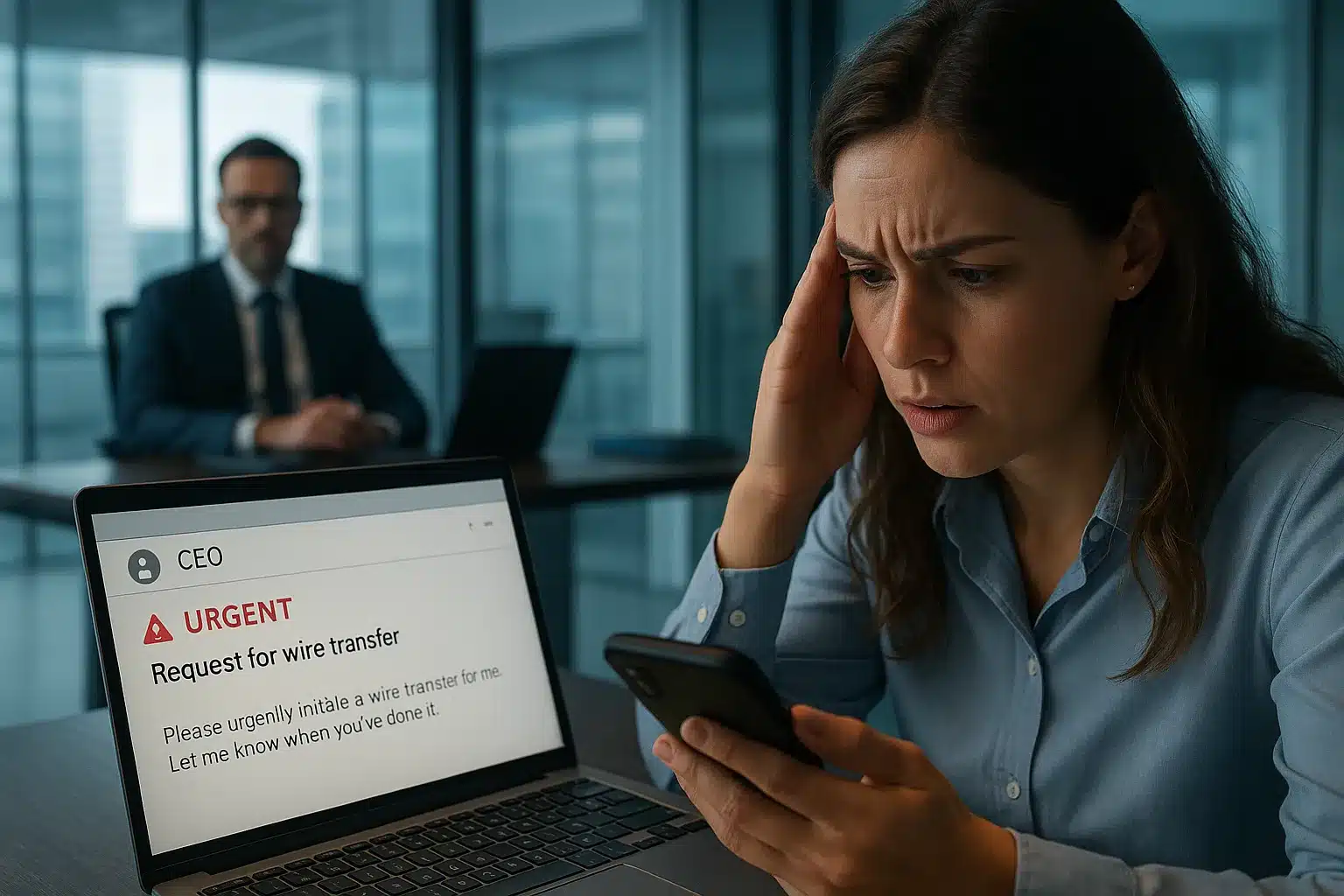
An employee receives an email that looks, sounds, and reads like it’s from your CEO. Under time pressure, they approve a wire transfer. $200,000 is gone before anyone realizes what happened.
This is social engineering in 2025. It’s not crude phishing; it’s sophisticated impersonation powered by AI-driven tonality replication.
Ready to Close Your Social Engineering Coverage Gaps?
The $250,000 Limit Problem
Most cyber insurance policies include social engineering fraud coverage, but cap the limit at $250,000. That sounds reasonable until you examine your actual exposure.
A single successful BEC attack against a mid-size company routinely exceeds that threshold. If your payment volumes are significant, the default limit leaves a dangerous gap between what your policy pays and what you actually lose.
Real-World Scenario:
You’re a $50M revenue company. A successful BEC attack results in a $400,000 loss. Your cyber policy covers $250,000. You pay $150,000 out-of-pocket. If you process significant payments or handle significant vendor relationships, your exposure could easily exceed the standard limit.
BEC Financial Impact by Business Size
According to the FBI’s IC3 2024 Annual Report, BEC complaints totaled 21,442 with losses approaching $2.77 billion, making it the second most costly cybercrime category after investment fraud.
Most SMBs never assess whether their social engineering fraud limit matches actual exposure until after they’ve been hit.
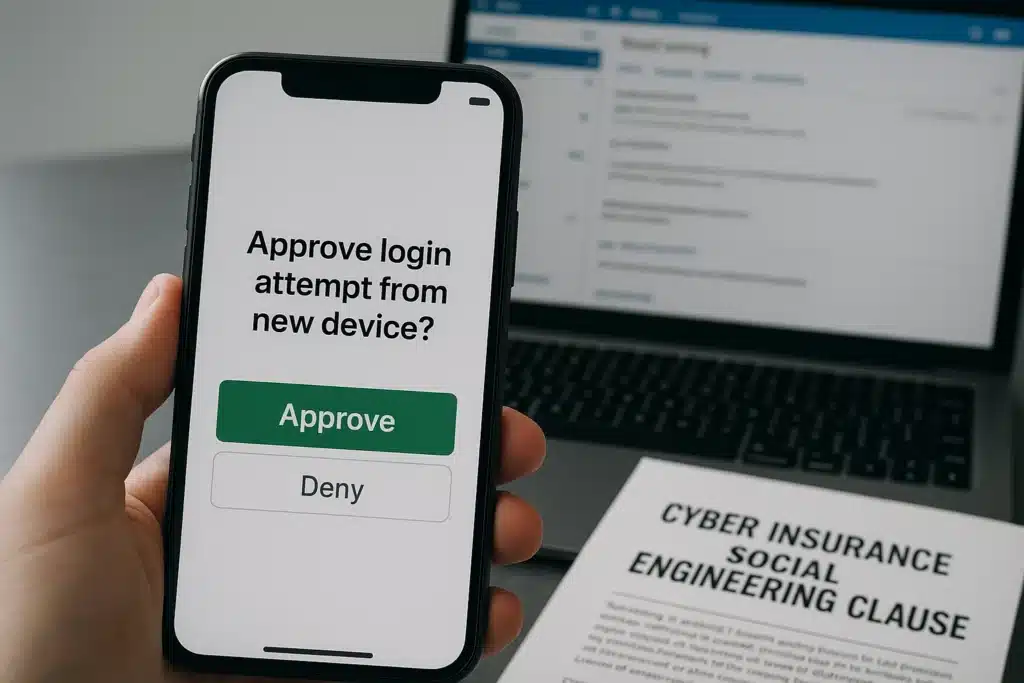
Coverage Conditions: Dual Authentication and Security Requirements
Social engineering coverage isn’t unconditional. Most policies require you to maintain specific controls to trigger coverage. The most common: dual authentication (multi-factor authentication).
If your policy requires dual authentication on critical accounts, and you don’t have it enabled, your coverage might be voided or limited.
The carrier’s logic: you had a reasonable security control available and didn’t implement it, reducing their liability.
Mandatory Security Controls
Required for coverage activation:
According to Microsoft security research, MFA blocks 99.9% of automated account attacks, which is why insurers now treat it as non-negotiable. Failure to maintain these controls consistently can void coverage when you need it most.
What Insurers Check Before Approving a Social Engineering Claim
Claim Element |
What Insurers Verify |
Where Disputes Arise |
|---|---|---|
|
Deception |
A fraudulent communication directly misled an authorized employee |
Was the deception the proximate cause, or did the employee act independently? |
|
Direct financial loss |
The deception caused the actual transfer of funds |
Carriers argue the employee, not the attacker, caused the loss |
|
Authorization |
The employee had authority to execute the transaction |
Disputed when access controls weren’t properly segmented |
|
Timely reporting |
Incident reported within 24–72 hours of discovery |
Late reporting triggers automatic denial |
|
Control compliance |
MFA and required security controls were active at time of loss |
Most common reason social engineering claims are voided entirely |
Understanding Your Social Engineering Fraud Limit
Your social engineering fraud limit determines the maximum your carrier pays per incident, not per policy period. Most businesses discover this limit is fixed at $250,000 by default, regardless of their overall policy limit. Understanding what’s covered, what’s capped, and what conditions apply prevents surprises at claim time.
What’s Covered
Financial losses from social engineering attacks where someone is tricked into transferring money or authorizing payments. CEO fraud, vendor impersonation, fake invoice schemes, payment fraud, typically covered under the social engineering fraud section of your cyber policy.
What’s the Limit
Most policies cap coverage at $250,000. Some offer higher limits ($500,000 or $1,000,000) if you pay additional premiums or demonstrate strong security controls.
What Are the Conditions
You must maintain controls (dual authentication, email security) and follow reporting procedures if an incident occurs. Failure to maintain controls impacts coverage.
What’s Your Actual Exposure
Critical question:
Is your potential social engineering fraud loss higher than your policy limit? If you’re a $30M revenue company processing hundreds of thousands in vendor payments monthly, your exposure could easily exceed $250,000 in a single attack.
Key Coverage Gaps to Address
How The Coyle Group Approaches Social Engineering Coverage Adequacy
Most SMBs don’t think about social engineering coverage limits until they need the coverage. By then, it’s too late. We work with businesses to close that gap proactively, assessing actual payment volumes, modeling realistic attack scenarios, and securing limits that match exposure through carrier negotiation, separate crime policies, or layered solutions.
We assess your actual social engineering fraud exposure:
Through that assessment, we determine whether your current coverage limit is adequate. If not, two options:
Option 1: Increase Limits Within Your Cyber Policy
We negotiate with your carrier to increase your social engineering fraud limit. This typically involves additional premium ($1,000–$5,000+ annually, depending on the increase requested). Not all carriers will increase limits significantly, but it’s worth asking.
Option 2: Add a Separate Crime Policy
A crime policy includes coverage for employee fraud, theft, and social engineering fraud. Limits on crime policies are often higher than cyber policies, and they layer on top of your cyber coverage. If cyber covers the first $250K and crime covers up to $500K additional, you have $750K in total coverage.
Client Example:
A financial services client had a $250,000 social engineering limit on their cyber policy. We assessed their exposure and realized they process $2M+ in wire transfers monthly. The potential loss from a single successful BEC attack could exceed $500,000. We negotiated an increase to their cyber policy’s social engineering limit (additional $3,000 annually) and added a $1,000,000 crime policy on top. They now have $1.25M in combined coverage, aligned with their actual exposure.
Our Assessment Process
This is critical because social engineering attacks are increasing in frequency and sophistication. Relying on the default $250,000 limit is a significant risk for most SMBs.
95+
Years of Family Legacy in Insurance
40+
Years Personal Experience
95%
Client Retention Rate
600+
Educational Videos
Real-World Defense Strategies
Beyond insurance, implementing robust controls reduces both attack success rates and premium costs. Strong email security, strict payment verification procedures, and documented employee training don’t just reduce your attack surface; they directly affect your insurability, your premium, and your ability to collect when a claim is filed.
Email Security
Payment Procedures
Employee Training
According to the FBI IC3, BEC remains a sophisticated threat targeting businesses performing wire transfers. Training employees to recognize manipulation tactics is essential. This includes understanding how social engineering works and maintaining vigilance even with familiar contacts.
Questions About Social Engineering Coverage
Protect Your Business From Social Engineering Fraud
Social engineering attacks are increasing in frequency and sophistication, and most businesses discover they’re underinsured only after an attack succeeds. Your cyber policy probably includes social engineering coverage, but that default $250,000 limit rarely matches actual exposure.
At The Coyle Group, we’ve helped hundreds of businesses close this dangerous gap. We assess your actual payment volumes, calculate realistic worst-case scenarios, and secure the coverage limits you actually need, whether through policy negotiation, separate crime insurance, or layered solutions.
Our process is straightforward: understand your exposure, compare it against your current coverage, and fix the gaps before an attack happens. If you’re processing significant wire transfers, handling vendor payments, or managing client funds, let’s verify your protection is adequate.

This article was written by Gordon B. Coyle, CPCU, ARM, AMIM, PWCA, CEO of The Coyle Group, who has over 40 years of experience working with business owners of all sizes and industries across the US, solving their insurance challenges. Gordon specializes in helping businesses develop comprehensive cyber insurance programs that protect against evolving threats.
Here’s how to take the next step
Schedule Your Insurance Confidence Assessment
In our 30-minute call, you’ll discover:
Not ready for a call?
Get Free Access to Our Gated Video:
“How to Finally Feel Confident in Your Coverage. “
And discover the exact system we use to help business owners eliminate hidden coverage gaps, stop overpaying, and finally feel confident in their protection.
What Peace of Mind Looks Like
Trusted by business owners across the U.S.
Want to know more?
See related blogs

The Crowdstrike Debacle and Cyber Insurance
Tech E&O vs. Cyber Insurance: What You Need to Know

First Party vs Third Party Cyber Insurance: What’s Covered, What’s Missing, and What You Actually Need



